“The Sony MicroVault USM-F fingerprint reader software that comes with the USB stick installs a driver that is hiding a directory under "c:\windows\". So, when enumerating files and subdirectories in the Windows directory, the directory and files inside it are not visible through Windows API. If you know the name of the directory, it is e.g. possible to enter the hidden directory using Command Prompt and it is possible to create new hidden files. There are also ways to run files from this directory. Files in this directory are also hidden from some antivirus scanners (as with the Sony BMG DRM case) — depending on the techniques employed by the antivirus software. It is therefore technically possible for malware to use the hidden directory as a hiding place.”
And more news about Sony being bad were to follow. F-Secure added that this was far from an isolated incident; the company also tested the latest MicroVault (available on Sony’s site) and found out that the software featured the same hiding functionality.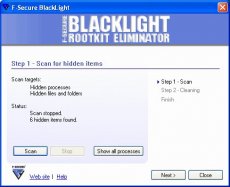
Still, there is something to be said on Sony’s account too. Apparently, the hidden folder was designed to “somehow protect the fingerprint authentication from tampering and bypass.”
On the other hand, rootkit is still rootkit and a new scandal is just waiting to happen, especially given Sony’s previous history. As you may recall, Sony was in a lot of hot water back 2005 due to copyrights protection software installed on the company’s music CDs, software which opened security holes for worms or viruses to later exploit.
Up till now Sony chose not to comment on F-Secure’s findings.



